Because people hate reading, I will just simplify this and then get into it a bit deeper.
1- Get a password manager, and use it!
2- Use unique, long and strong passwords (with a couple of exceptions) with 2FA.
3- Stop coming to me if you don’t listen, I am tired of solving your stupidity.
Psst! This blog post has a unique podcast style audible version at the end. You don’t like reading? Check out the video!
Yes, I am being rude, but I continue to receive weekly requests to help people out with their account problems online. And while I love to help my family and friends, it’s not needed. I am literally wasting my time. Because despite that I harp on this over and over again: You still use the same easy to guess password everywhere. Or you simply don’t use a manager and you can’t even remember which email you’ve used to sign up with in the first place.
And how do I solve this problem for you? I hack you. Basically. And it’s not even a hack. I just go online and check known sites where they have multiple gigabytes of databases with your email address in it. And trust me: It’s in there. If the password is old, I just wait two months, because another big site will leak their data and we have the newer one.
How is that even possible? Simple: Websites don’t always anticipate their success. They start with an idea, put a user system to it, apply basic authentification and then go through stages of upgrades and updates. But security isn’t being taken serious. They think encryption is fine. Well, sure, it can be. If you don’t store the decryption keys on the same system. They get hacked, and yep, the hackers just decrypt the data using the key provided by the company itself. Or, they only use an old hashing system. Their developer thinks md5/sha1 hashing is ‘good enough’, but it’s so outdated you can just look it up on a rainbow table (as they call it) and match a hash to a known entry. There are numerous examples like this. And trust me: malicious users target popular sites. And they do get in. Ask Facebook, ask LinkedIn, ask Twitter, ask PayPal, ask your bank for crying out loud.
It’s annoying, and it’s harder, and more time consuming to have different passwords for various sites with additional layers of security, and extra encryption or hardware keys for two step authentification, or an app on the phone for two factor auth. But sorry, it’s what is needed.
Who cares! I got nothing to hide. Is that a challenge? Want me to tell your husband who you’re actually talking to on Facebook msg? Because you use the same password on a gaming website that stored their passwords in plain text? Want your boss to get copies of your emails about your political opinion (where you’re not holding back because you think you’re talking to a brother or whatever) and your email password is the same as that LinkedIn password from a few years ago? Imagine how long malicious people might have already been inside your accounts and you haven’t even noticed. Just waiting for you to share your credit card details with your dad who needs help online.
Stop scaring me! Sorry, I am not. It’s the reality of the world we live in. And malicious people don’t care about you – they care about your identity, your PayPal login that’s linked to your bank with a 50,000 credit limit. They care about your business account for insider information to make stock choices that can ruin your boss’ company and make them rich.
Ignoring it is fine, as long as nothing happens. But don’t call me anymore please to help you out when it goes wrong. I’ve done it for so long and by now the Internet has matured enough that it’s mainstream to every generation. All our operating systems are online, with in the cloud features, syncing, family sharing, etc. Your grandma on her iPad watching Netflix.
When something happens now, I just want to say: You knew this, you’ve chosen to ignore it. Please contact me before anything happens – so we can talk privacy and security and help lower the risk of compromise, lower the damage, help you stay in control a bit more.
So 1. Get a password manager. They’re much more affordable than the damage from a stolen identity. And they are cross platform these days as well. Get a family account, so you can help yourself and your family members. Just write down in a login the name of the thing you signed up on, the url to find it, the username you created, which email you signed up with. What password you set, which security questions and answers, write down those 2fa backup codes, if you can turn on 2FA and note down that you have 2fa turned on or off.
2. Most password managers hook into the browser, you can just copy paste long, strong, unique passwords of 32 characters of shit and never remember them. You have an app that works and does it.
Which app? 1password (from agile), get the stand alone version.
3. If you do desire to get some help, I’d love to help. I have no problem giving you security and privacy advice on the Internet. I am always open to help share what I have learned myself.
Oh, and you’re so perfect? No, my details are out there as well. Because I sign up on loads of sites and they all get compromised and have their data leaked online – nothing I can do about that. But I moved to 1Password, and use 32+ character long strings – and I change them every 6 to 12 months. And I’ve been using a password manager for years now. Which is why it’s such a surprise to me that you haven’t yet. I blog about this every year, I tweet about that every year. I post warnings on Facebook, every year! When are you going to finally take your online presence a bit more serious?
(Don’t get me wrong, in case of a compromise or data leak you are not at fault, you’re the victim, but instead of panicking if your password that’s now public is going to be a problem, you should ‘only worry’ and you should only have to change it knowing it didn’t affect your banking, email, business accounts, etc)
How to get 1password? I want to be clear, many password managers out there use their own site for sharing the vault with your data. I am utterly against that. Agilebit has changed in the last year to a subscription model and I am not too happy about that. I want the vault on my systems and my systems alone. There’s no need to put it on Dropbox, iCloud, or Agile’s own servers. No matter if I hold the decryption keys and they claim they’re the best in the business. I’ve learned to never trust anybody. (Thank you Steve Gibson “trust no one” TNO) But 1Password is the only one who does properly secure the data you enter in the vault. And their apps work on Android, iOS, Mac, Windows, .. and they still sell the standalone version.
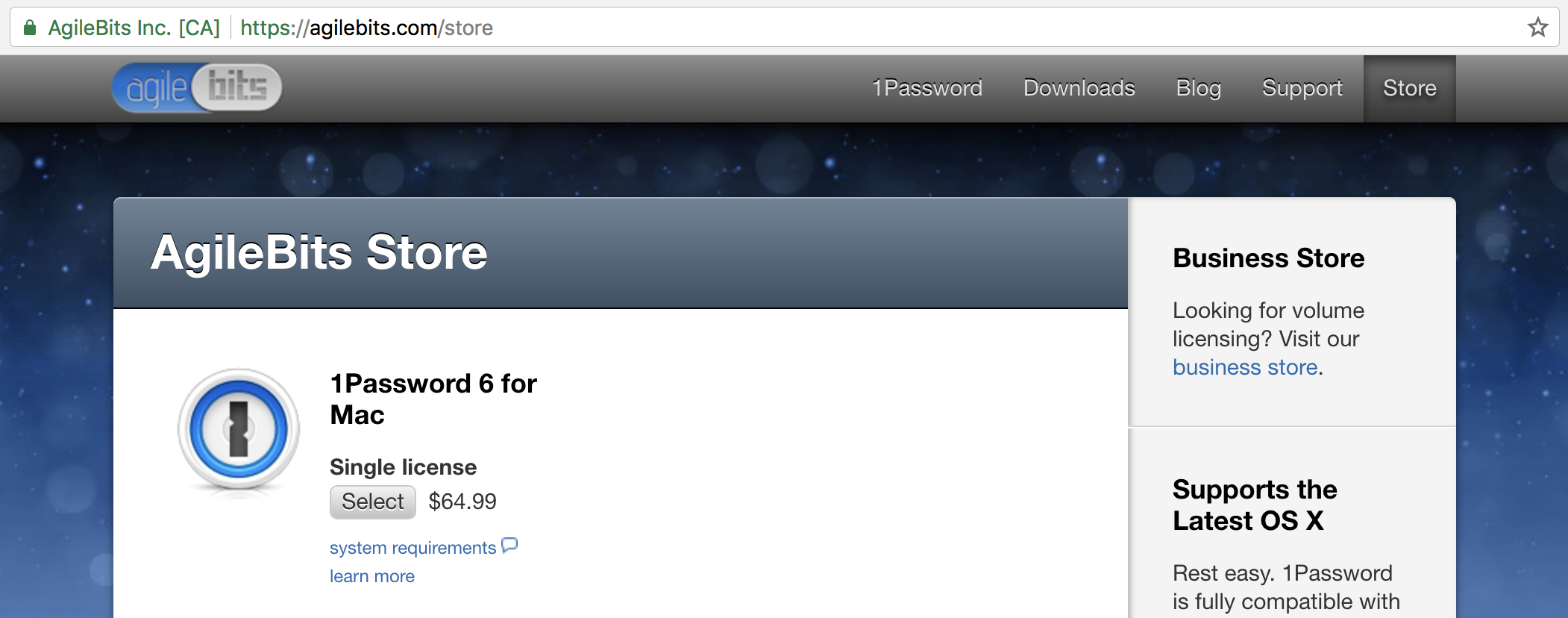
They’re hiding it on a phycologically ugly old page away from their frontpage. But you can get it here:
https://agilebits.com/store
However, they do sell the subscription model if you trust that. You will have more convenience of them handling a lot of the backend, but in exchange you give them your data in a vault to access through the web as well. What you do is your choice, but this year I still recommend to sync local over your lan with the standalone 1Password version on a Mac and with iOS.
One reason I am against giving them my vault is when they said (not a direct quote) “it doesn’t matter if we get compromised, if the malicious people have your vault they still cannot get into it”. Yeah.. famous last words. Who cares if I am the only one with the master password, and that they cannot get into it. That blob of data is still my whole life – every account and bank details, credit cards, etc that a malicious person has a copy of. I want to know there are 3 copies, one on this mac, one on my iPhone and one in my mind. Go with the standalone.
Anyway, I am going on a tantrum (and I can! this is my blog, *scoffs*)
There are a few exceptions to my preaching, when it comes to unique and long strong passwords of a billion characters, etc. The master password. Your Apple ID, .. stuff that when you think about it you can NOT copy/paste from a password manager. Through examples: You can not get a copy of your Apple ID from the password manager if you can’t download the app on a new device. You have to login to your Apple ID to download the app in the first place. (Yes, there are ways around that obviously) And you can’t get a copy/paste of the password managers’ master password because you need to open the app first. Duh moment here!
In those cases I do recommend to either apply common sense to create something that you know and others can’t brute force too easily. Avoid mega complex long strings that you can forget, because you shouldn’t forget those important passwords. But of course, these passwords obviously do matter, they are the access to so so much more. Your Apple ID should be strong and unique, but not too complex that you can’t figure it out. So either have it also on the app on your phone so you can read it from the screen and still semi easily type it over, or write it down somewhere and store that in a safe place.
And I can get technical here, because there are more of these situations: Start your computer (you need a bios password), your operating system loads (you need to login to your account), you mount a hard drive (it’s encrypted, you need a password for that), and you need to get into iCloud (your apple id is needed a lot), and your password manager (has a master pass you need). After all that, you’re ready to get into your email finally.. PFF, but let’s keep it simple. I know almost nobody cares about their precious data they don’t back up (yes, I judge all of you!) so nobody has a strong computer login, almost nobody has full disk encryption, and nobody has a bios password set. So I am sticking in this blog post to your master password and the apple id. (if you’re on windows, you’re in a whole different world of pain, please please use a password manager).
Anyway, my point was that there are a few exceptions. And that managing your online presence isn’t easy or convenient. But it’s a lot easier than problem solving.
Wow, made it to the end! Thank you for reading, and despite my cynical look on things, or my negative attitude: I mean well. I want you to not be a victim of data leaks and account compromises, and I could go on for hours – but it starts with taking your online presence serious and using a password manager.